First, it does not involve physical conflict using kinetic weapons, which removes direct bloodletting from the equation. Second, it can target critical infrastructure (power grids, water supplies) as well as the command, control, communications, computing and intelligence (C4I) capabilities of adversaries. Third, it can be masked so that perpetrators can claim a measure of plausible deniability or at least intellectual distance from the action. Fourth, it can be used for tactical and strategic purposes and the pursuit of short or long-term objectives.
Much like military drones, cyberwar is here to stay.
The war is not one sided: Russian hackers have penetrated Pentagon email networks and the 5 Eyes signals intelligence alliance has dedicated hacking cells working 24/7 on targets of opportunity. Many other nations also indulge in the practice as far as their technological capabilities allow them. To these can be added a host of non-state actors—Wikileaks, Anonymous, ISIS, among others—who have also developed the capability to engage in electronic espionage, sabotage, data capture and theft.
With the most recent revelations about the hacks on the US Office of Personnel Management (OPM) archival records (which include personal details of active and retired federal employees as well as identities of those who have had or hold security clearances, perhaps including myself given my prior employment by the Department of Defense) an evolution in cyber warfare is now evident.
Previously, most state-sanctioned cyber attacks were so-called “front door” attacks on government or corporate mainframes, servers and networks. The interest was in surreptitiously obtaining sensitive data or installing surveillance devices in order to engage in ongoing monitoring of targeted entities. “Back door” probes and attacks were the province of non-state actors, especially criminal organisations, seeking to obtain private information of individuals and groups for fraudulent use. However, the recent attacks have been of the “back door” variety yet purportedly state sanctioned, and the Snowden leaks have revealed that 5 Eyes targets the personal communications of government officials, diplomats, military officials and corporate managers as a matter of course.
The move to state-sponsored “back door” hacks is ominous. Accessing data about current and retired government employees can be used to blackmail those suffering personal liabilities (debt, infidelity) in order to obtain sensitive information about government processes, procedures, protocols and policy. It can target active and former intelligence and military officials and others with access to classified information. It can target former public officials that have moved to the private sector, particularly in fields of strategic or commercial importance. Likewise, obtaining sensitive personal data of employees working in private firms opens the door to similar exploitation for illicit commercial gain.
Advances in consumer telecommunications have made cyber hacking easier. Smart phones and their applications are considered to be the most vulnerable to hacking. Because many people store an enormous amount of personal data on these devices, and because they often mix work and personal business on them, they represent an enticing entry point when targeted. Yet even knowing this millions of consumers continue to pack their lives into electronic devices, treating them more as secure bank vaults rather than as windows on their deepest secrets. Not surprisingly, both state and non-state actors have embarked on concerted efforts to penetrate mobile networks and hand-held devices. Encryption, while a useful defense against less capable hackers, only slows down but does not stop the probes of technologically sophisticated hackers such as those in the employ of a number of states.
The bottom line is this: the smaller the telecommunications market, the easier it is for cyber hackers to successfully place backdoor “bugs” into the network and targets within it, especially if government and corporate resources are directed towards defending against “front door” attacks. On the bright side, it is easier to defend against attacks in a smaller market if governments, firms, service providers and consumers work to provide a common defense against both “front door” and “back door” hacking.
The implications for the South Pacific are significant.
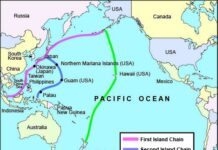
In this new battleground physical distance cannot insulate South Pacific states from foreign attack because cyber-war knows no territorial boundaries. Countries like Australia and New Zealand provide inviting targets because not only are they integral and active members of Western espionage and security networks, but they also have proprietary technologies and intellectual property in strategic sectors of their trade-dependent economy (including niche defense-related firms) that are of interest to others. Similarly, French Polynesia and Melanesia have strategic importance as projection points for French power (including intelligence gathering), while Fiji is considered a vital waypoint for South Pacific lines of communication, including telecommunications as well as shipping. Smaller Pacific island states have increasingly become the object of investor attention in fisheries and previously unaccessible resources such as seabed minerals and offshore fossil fuel deposits, while the larger Melanesian counterparts, Papua New Guinea and the Solomons Islands, have seen heavy foreign investment in resource extractive enterprises. This has raised the strategic profile of the South Pacific, which in turns it into an arena of contestation for rival powers.
The rise in the South Pacific’s strategic profile has attracted the attention of larger competing states, particularly China, India and the Anglophone countries grouped in the 5 Eyes signals intelligence network. That has made telecommunications security a growing concern because if nothing else South Pacific corporate, academic and public service elites are relatively small and the overlap between them quite extensive, something that makes hacks on their personal data are a valuable tool of those who wish to use them for untoward purposes.
South Pacific public agencies and private firms have been relatively slow to react to the threat of cyber warfare. The data they hold on their employees, managers, policy elites and general population is an inviting “back door” for determined hackers seeking to exploit vulnerabilities in regional cyber networks. Since many South Pacific citizens are lax about separating their work and private electronic correspondence and records, the potential to access sensitive personal information is high.
Australia and New Zealand have been the subject of numerous “front door” cyber attacks and probes on public and private agencies, including an attack by Chinese-based hackers on New Zealand’s NIWA supercomputer carried out in concert with a similar attack by the same source on the supercomputer run by the US National Oceanographic and Atmospheric Administration (NIWA’s US counterpart). Australians and New Zealanders have been the targets of numerous “back door” intrusions such as phishing and other scams perpetrated by fraudsters and conmen. Yet successive governments in both countries have been relatively slow to recognize the new threats advancing towards them in the cyber-sphere. For example, only recently did New Zealand create dedicated cyber security cells within the intelligence community and just last year did it get around to amending the Government Communications Security Bureau (GCSB) Act to address vulnerabilities in domestic internet security. But that still may not be enough.
Until South Pacific states resolve the problem of institutional lag (that is, the time gap between the emergence of a technologically-driven threat and an institutional response on the part of those agencies responsible for defending against it), there is reason to be concerned for the security of private data stored in them. After all, in the age of cyberwar there is no such thing as a benign strategic environment.
Advisory.
36th Parallel Assessments does not offer specialised internet technology (IT) security services. However, it can offer simple tips derived from counter-intelligence operational guides for those concerned about the security of their private information. These can be grouped together under what can be called the “Battlestar Gallatica” (after the cult TV series) defense: when confronted with a “high tech” sophisticated telecommunications-channeled threats, it is best to go “low tech.” In this context “low tech” information security means returning to oral and paper records and electronic data that is removed from the cyber sphere. Paper records should not be digitalised and should be stored in old fashioned safes or security vaults. Oral conversations should take place on (preferably non-registered or unisted) land lines or in person. Mobile devices and/or “smart” video equipment should be changed regularly and be removed from rooms in which sensitive conversations are held (turning them off does not ensure that they cannot be remotely activated). Electronic files should be stored on computers and flash drives not connected to the internet (care should be taken when transferring materials on flash drives that may have been exposed to internet-connected computers). Secure couriers should be used to exchange sensitive information.
This may appear old-fashioned and inefficient, but it has the value of raising the physical costs to those wishing to illicitly access such information. Again, the bottom line is that modern telecommunications devices should be treated as windows on intimate moments or confidential thoughts rather than as easy ways of conveying information. By shutting these windows via the use of “low tech” alternatives a measure of information security can be achieved that is no longer possible in cyberspace.
36th Parallel Assessments offers policy makers risk analysis of their cyber vulnerabilities as well as the larger strategic context in which they exist. Please contact us for more details about our services.